HackTheBox: Optimum
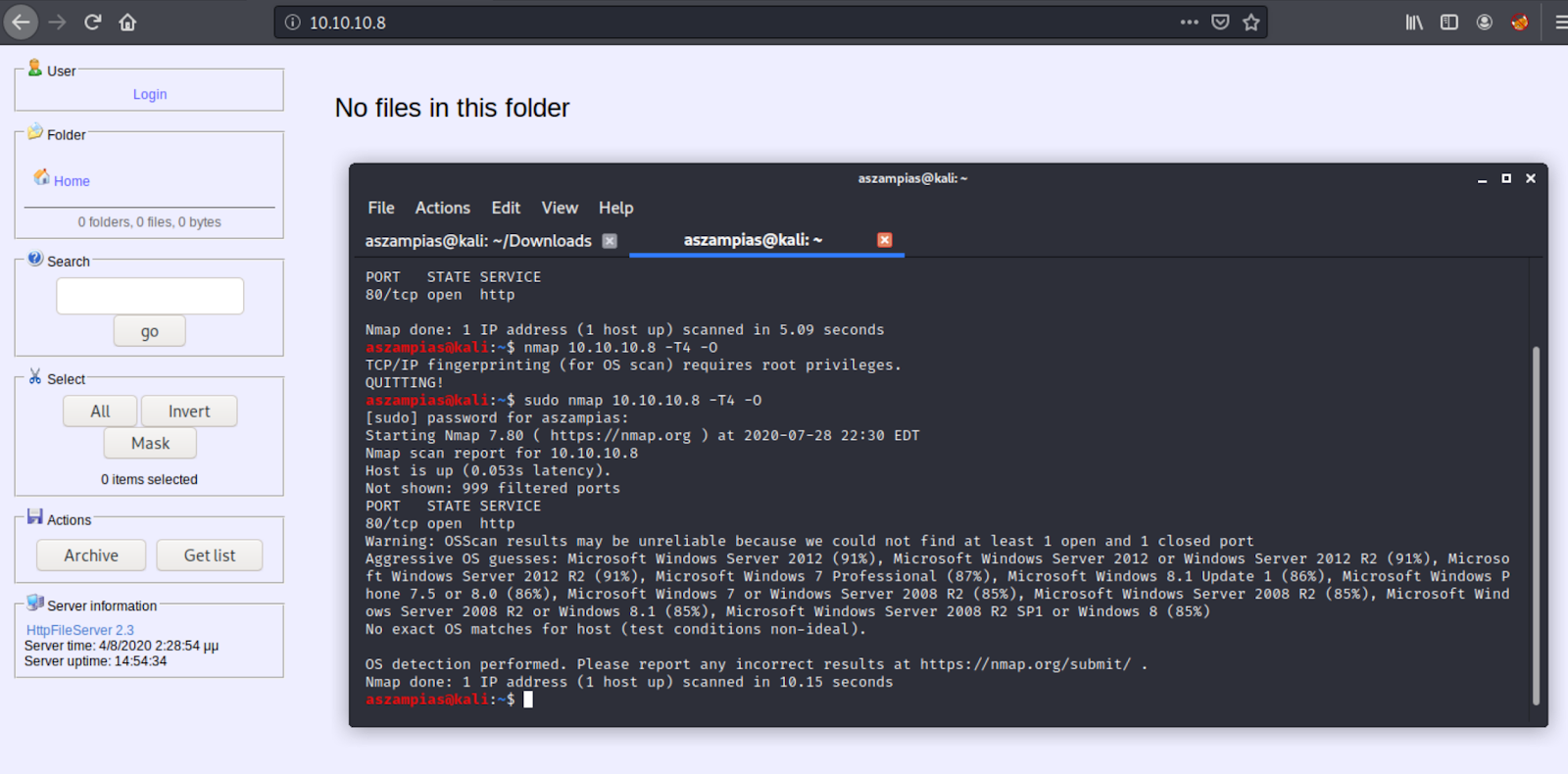
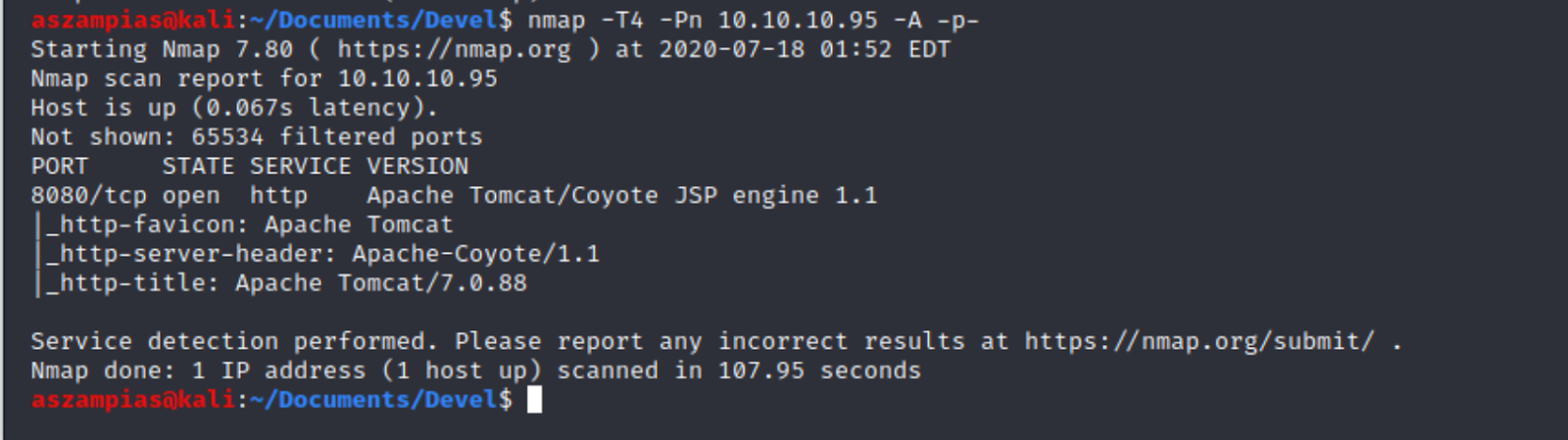
HTB Optimum Writeup The first thing I notice is an HTTP server is up. It looks old. I'm gonna copy "HttpFileServer 2.3" and see what I get in Google: Well that was easy. Didn't even have to put "exploit" at the end. Lets check out the Rapid7 page. The page points to a metasploit exploit called "exploit/windows/http/rejetto_hfs_exe". I'm gonna use that first. The exploit works and we can read user.txt on kostas desktop. The next challenge is privilege escalation. Then I import Sherlock.ps1 powershell.exe -exec bypass -Command "& {Import-Module .\Sherlock.ps1; Find-AllVulns}" I see that MS16-098 is vulnerable. We can download binary here: https://www.exploit-db.com/exploits/41020 And there you go!